For any organization prioritizing security, managing who can access physical locations or sensitive digital systems is paramount. Access control forms provide a vital framework, standardizing the entire process from requesting permission to documenting approvals. This systematic approach not only enhances oversight and accountability but also proactively protects valuable assets, confidential data, and ensures a safer environment for all stakeholders.
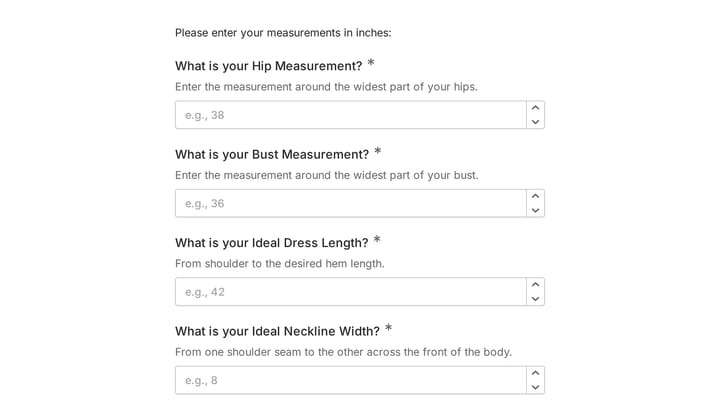
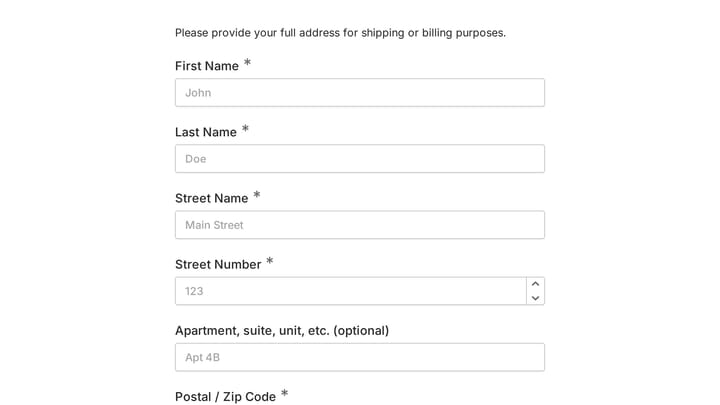
A well-designed access control form gathers all critical information to make informed decisions. This typically includes the requester's name, employee ID, and department, alongside a clear explanation of why access is needed. It also defines the type of access required – whether for a specific building, a restricted room, a software application, or a database – and the exact timeframe, including start and end dates. To ensure full compliance and security, many forms also incorporate fields for manager or security personnel authorization signatures, securing all necessary approvals before access is granted.
Adopting a digital access control form significantly elevates an organization's security posture. It creates an immutable audit trail of every request and approval, which is invaluable for compliance and regulatory reporting. This digital method drastically lowers the risk of unauthorized access and enables rapid identification of any inconsistencies. Beyond security, these forms streamline administrative workflows, automating the entire request process and empowering security or IT teams to manage permissions efficiently, free from the burdens of manual paperwork.